About 12 hours ago Apple dropped updates to two of its built-in security tools, the Malware Removal Tool (aka MRT.app) and XProtect.
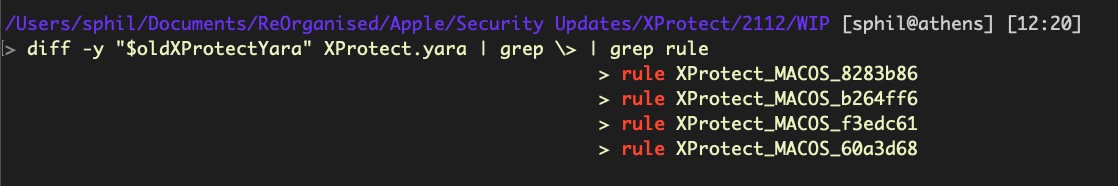
Most of the changes occurred in XProtect, with 4 new families added.
- MACOS.8283b86
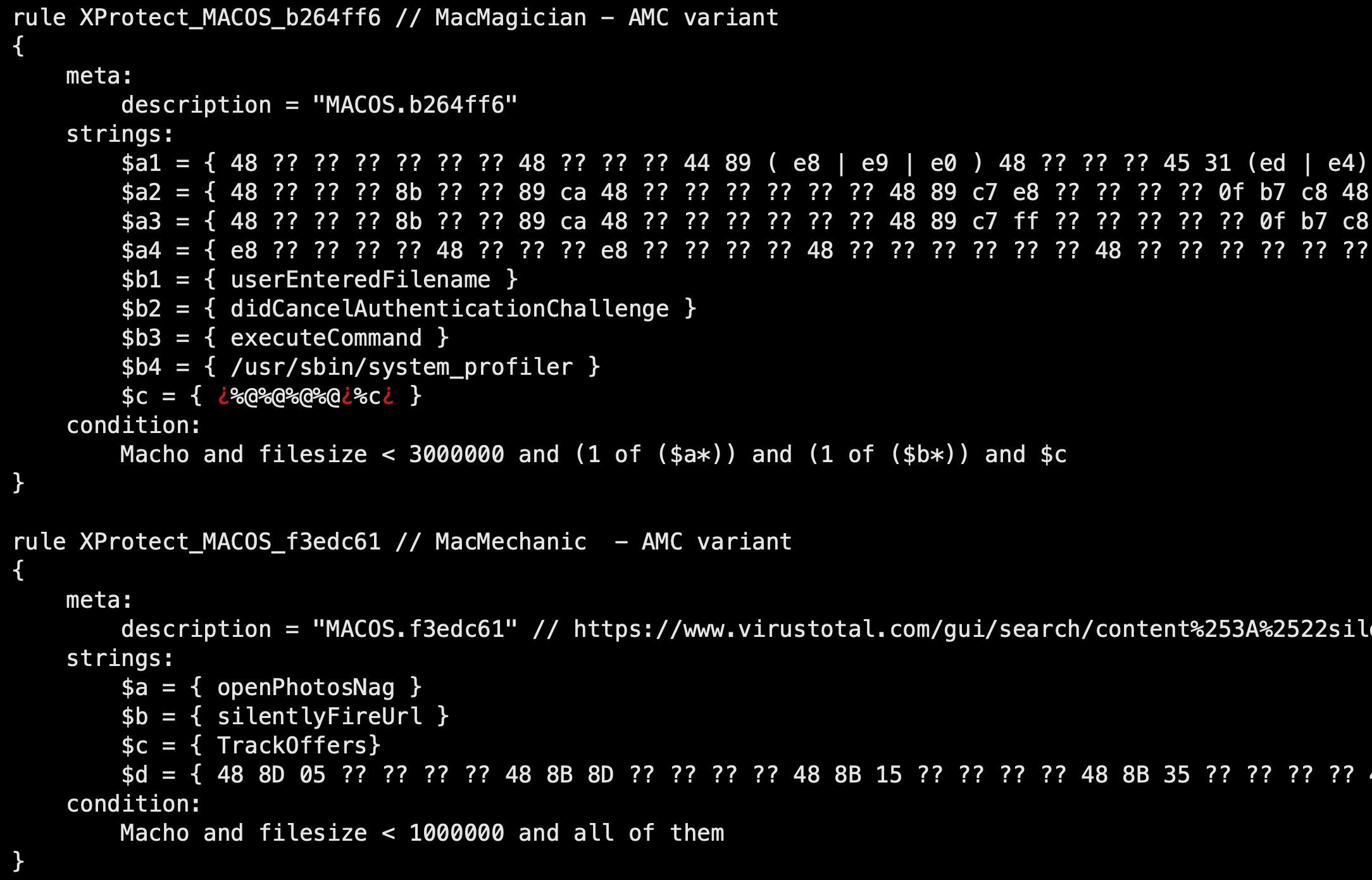
- MACOS.b264ff6
- MACOS.f3edc61
- MACOS.60a3d68
The first three detect a bunch of known PUPs (potentially unwanted programs) that variously go by the names of Mac Cleanup Pro, MacMagician and MacMechanic.
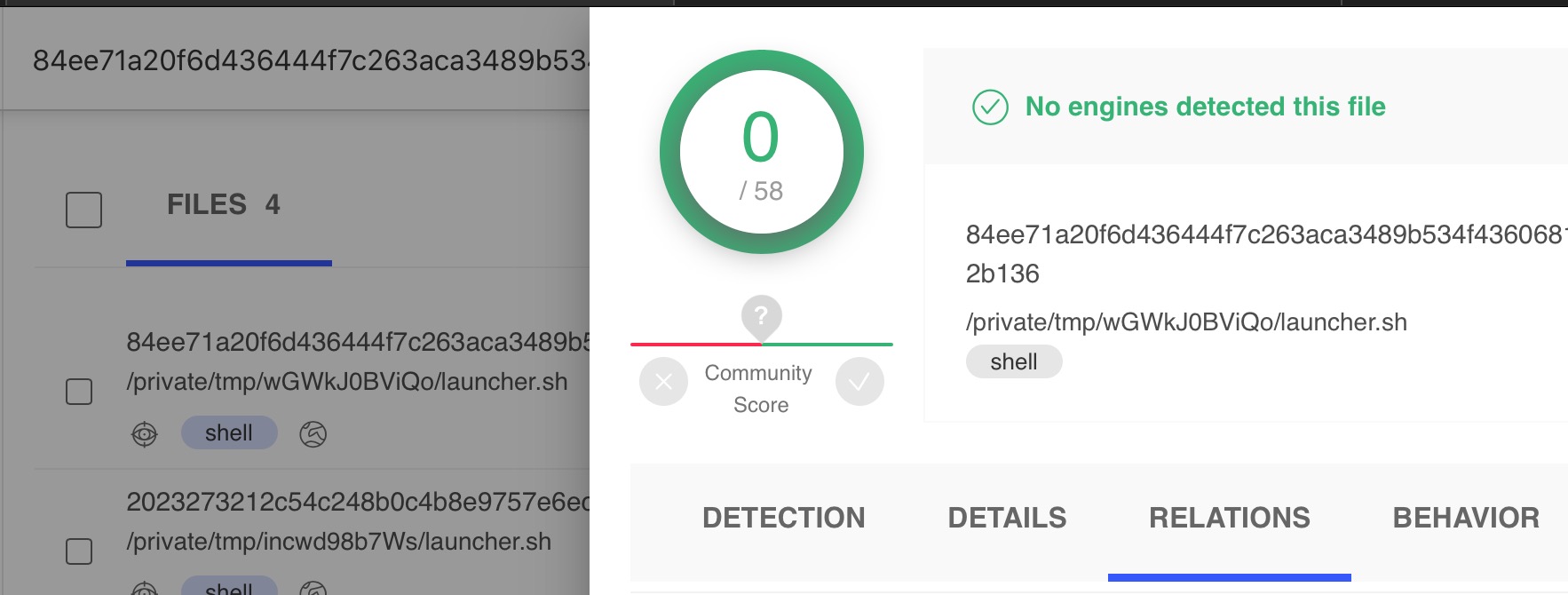
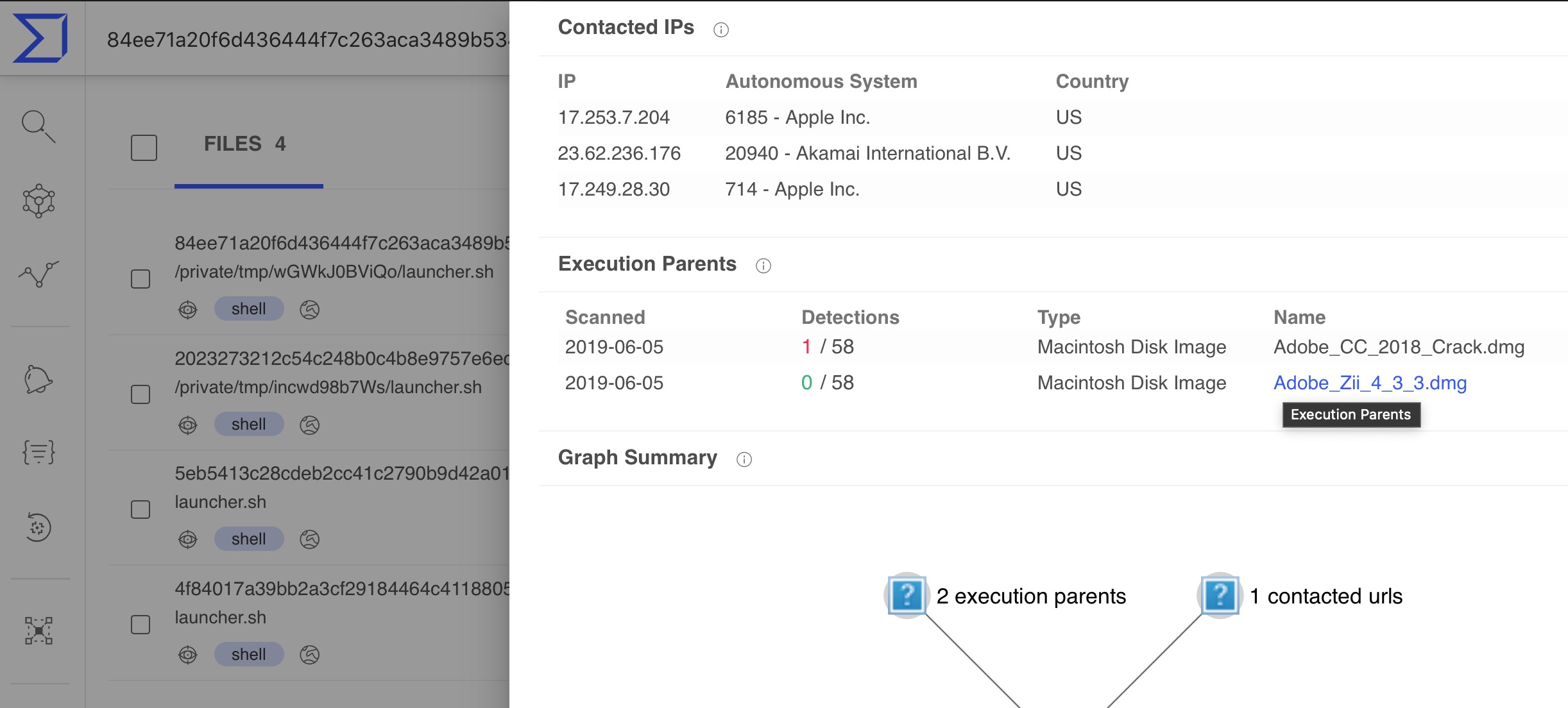
The fourth detection is more interesting as it looks for a shell script that appears to be related to OSX.Darthminer.
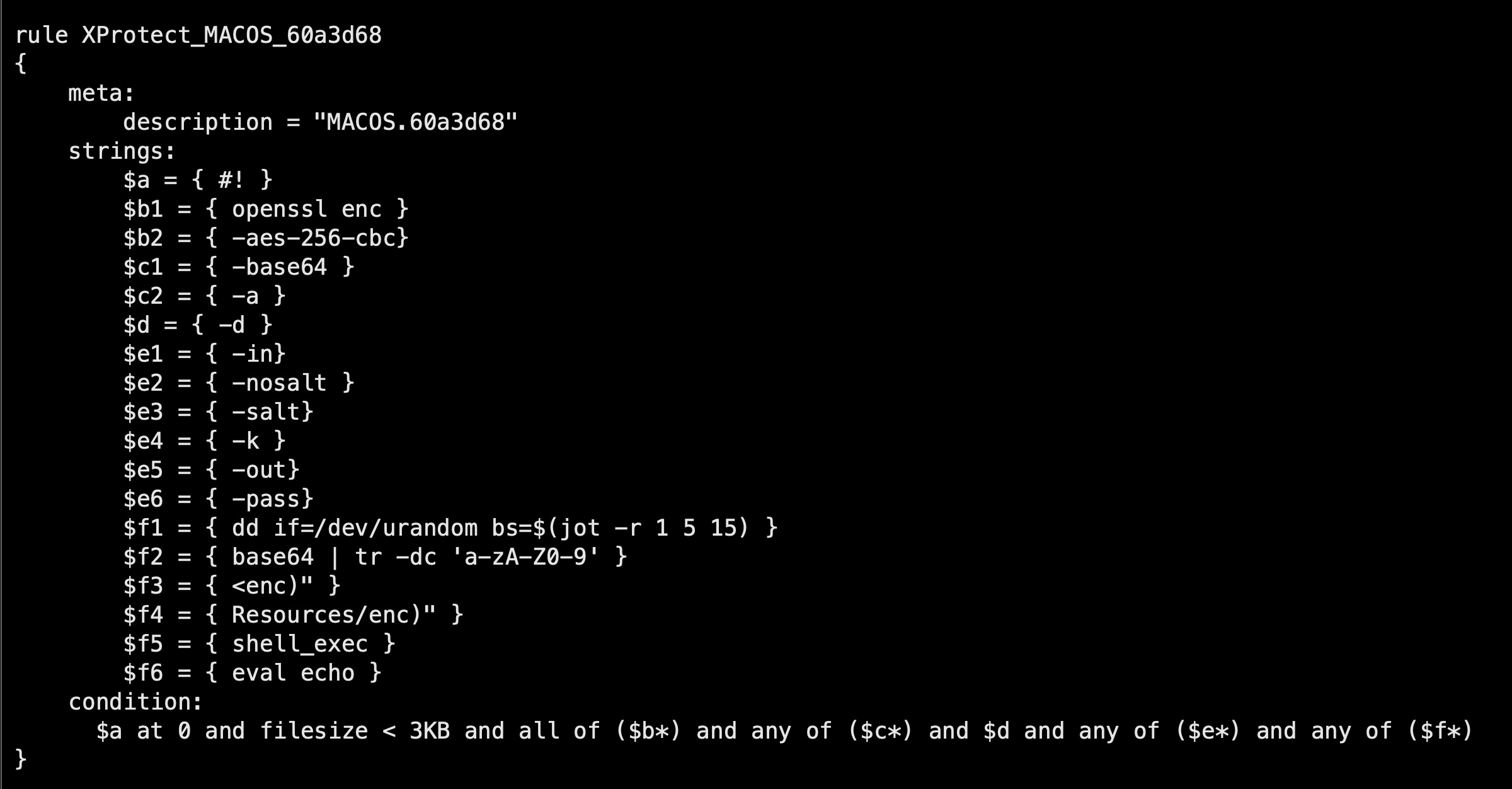
With a little help from VirusTotal, we can see that the rule detects a script that is related to Adobe Zii and Adobe CC cracked software used by OSX.Darthminer.
The update to MRT brings the “app that’s not an app” - because users can neither launch it nor do anything else with it, as indicated by the invalid icon - to version 1.53.
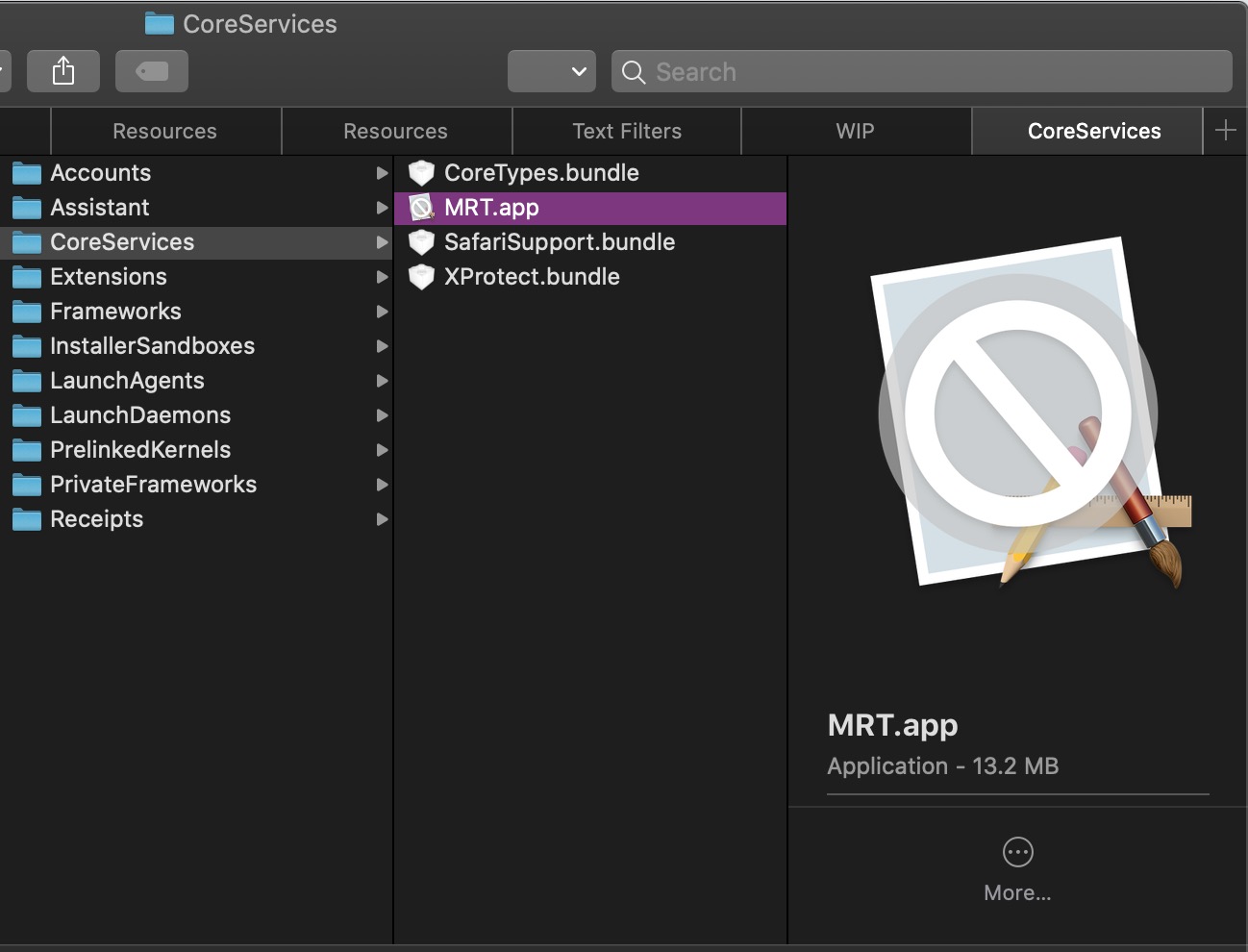
The new version adds a detection routine for what Apple internally call MRT.Family9dcbaf7. As for what MRT’s new family MRT.Family9dcbaf7 actually detects, stay tuned as we’ll be posting about that in a separate blog post. In the meantime, if you’d like to learn how to reverse and do diffs on the MRT.app yourself, see the post Running Diffs on Apple’s MRT app to get started.
That’s it for this update. 😀

